Where is The Safe Place for Your Cryptos on Post-Centralized-Exchanges Era?
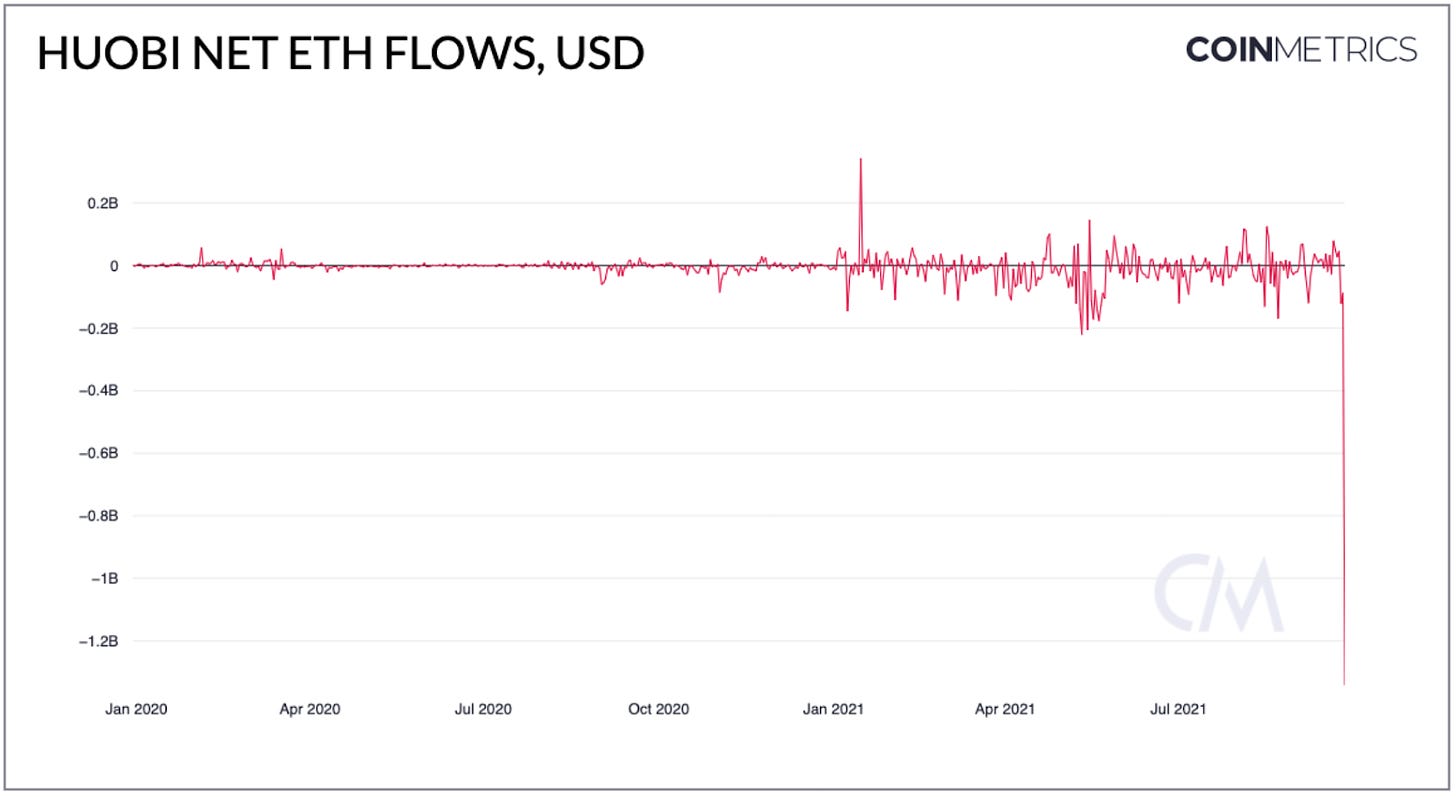
Along with the announcement from Huobi, one of the most well-established centralized exchanges (CEX) on their exit in the Chinese market, other exchanges have also taken similar measures. A large number of Chinese investors are withdrawing from CEXs. Reported by CoinMetrics, Huobi’s net outflow of ETH reached 440,000, about 1.76 billion USD, on 26th Sept, which set its highest record in the history.
Resource:CoinMetrics
And a large number of these crypto assets have entered decentralized wallets such as imToken and MetaMask. Unlike centralized platforms, the assets stored in these self-custodial wallets are not controlled and managed by the service providers, instead, only users are the ones who are capable of doing so.
It means only users themselves have control over the wallets, besides, no one can interfere your transfer or freeze your accounts. Worst case if wallet service providers have suspended their services, users still maintain the access to their funds by importing them to other wallets using the recovery phrases.
However, lots of investors ignore the security of the devices where the wallets are installed.
In fact, with the development of technology, it’s not difficult for hackers to steal information from smart devices (smartphones, tablets etc.). Assuming your phones are hacked by malware, the recovery phrase stored in your phones can be easily stolen and put your funds at risk.
According to a report by the cyber security company Intezer Labs, ElectroRAT, a Trojan imitating a crypto trading program, has affected thousands of users. It is disguised as a fake exchange and application, invades users’ devices, locates and transfers crypto assets. Thousands of wallets have been stolen so far.
For more information: Ryuk ransomware Bitcoin wallets point to $150 million operation
So how to avoid these situations from happening? Usually there are 2 approaches:
Make sure there is no malware in your smart devices.
It looks easy but hard to perform as many malicious softwares will disguise as ordinary ones, or hide behind legitimate Apps to avoid detection..
Cut off network
Completely shuts off the internet connection to eliminate the possibility of a hacker stealing your mnemonic or private key through the network.
A wallet disconnected to the internet is called a cold wallet. Compared to hot wallets, which are connected to the internet, cold wallets are immune to hacking and malware threats and have better security.
---
imKey Hardware Wallet is a professional cold wallet device incubated and deeply integrated by imToken, it ensures the mnemonic phrases never touch the internet by generating them offline and keeping them in the secure chip. In the crypto world, the mnemonic phrase is the only proof of asset ownership, so to keep your mnemonic safe is to keep your funds safe.
In blockchain industry, there is a best quote:
Small assets in software wallets, large assets in hardware wallets。
👆This is recognized as the best asset management solution in the industry.
Like imToken, it’s a software wallet, also known as hot wallet, only password is required when users are transferring funds. However, a hardware wallet is more likely a bank USB, every transfer must be authorized by imKey to better secure your assets.
imToken requesting imKey for authentication
Moreover, regarding hardware security, the grade of imKey chip has exceeded bank USB’s, reaching the military-grade which is CC EAL6+. CC is an international information security evaluation standard, there are seven levels from low to high, EAL1 to EAL7, the higher the level is, the more security guarantees the chip must meet, and means the higher security of the system.
You can think of the security chip as a safe for your mnemonic, how safe it is directly has an impact on your mnemonic phrase. imKey uses military-grade CC EAL6+ security chips, which can effectively prevent electronic attacks (SPA and DPA attacks), while other ordinary hardware wallets cannot prevent such attacks.
In terms of convenience, with imKey, you will be able to manage assets on 11 public chains such as BTC, ETH, COSMOS, TRON, EOS and mainstream EVM-compatible chains such as BSC, HECO, POLYGON, XDAI. you also have access to popular NFT, DeFi and Layer 2 DApps.
Your asset security is steadily guarded by imKey. What’s more, imKey is extremely portable as it’s only 2.3mm thick and less than 10g weight.
Blockchain security company SlowMist Technology partner and CTO Mr. Blue once commented on imKey:
From beginning to end, I have witnessed its project establishment and final production process, and even visited the factory to check the quality. imKey meets my personal security requirements on the hardware wallet.
SlowMist is one of the first companies to focus on blockchain ecological security . It has done security audits and defense deployments for many leading digital asset exchanges, wallets, public chains, smart contracts and other projects in the world.
---
The crypto currency market is full of ups and downs, book number varies as well. You certainly don't want to invest and gain income only to find out that your assets have been stolen, right? Then why don’t you keep an imKey from your daily fluctuations?
Visit our official store to bring your imKey home!